Web applications have become an option for many businesses, but a large number of web applications are vulnerable to various threats and attacks.
Web applications have become an option for different types of businesses and startups around the world to reach a wider audience and increase their sales. However, there are huge risks about data and other things when companies put their business on the web.
Every year, a large number of web applications are vulnerable to various threats and attacks. Therefore, companies need to understand some of the most common types of web application vulnerabilities.
Web Application Vulnerabilities
Vulnerabilities can occur in web applications because there is an error in the development or design process. Web application vulnerabilities are also obtained from internal and external attacks.
Vulnerabilities in web applications usually occur at the database level or network level. It also includes things like input errors or invalid input, problematic/bad web application design, etc.
SQL Injection
SQL injection can pave the way for an attacker to utilize malicious data installed to attack a specific database or directory. Injection will occur as soon as the attacker sends a query or command to the interpreter and forces the interpreter to perform it, where the command is unwanted and offers unauthorized data.
There are two ways that hackers implement SQL injection. The first is SQL injection to attack a database and the second is by using LDAP injection to attack a specific directory.
The attacker will insert malicious content with the aim of accessing or obtaining content or data in the database. By doing so, the attacker can access sensitive information or modify things in the database.
Cross-Site Scripting (XSS)
XSS is an attack on the client or user side. An attacker will insert a malicious script into a web page or web application. Then, the attack will start when the user accesses the web page or web application that has been installed with the script.
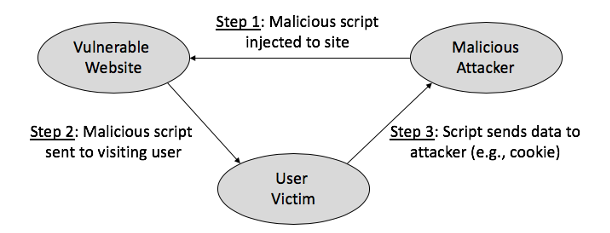
Source: helpnetsecurity
Because of this, the attacker can access all important information instantly or may even be able to trick users into revealing their own information.
By applying this attack method, the attacker will retrieve various things such as session cookies, browser history, web pages that have sensitive content, etc.
Broken Authentication
This vulnerability can allow an attacker to compromise all authentication details used by the user. Broken authentication terms can be caused by 2 main things: session management and credential management.
If these two things are not properly implemented in web applications, it will cause serious vulnerability issues such as credential stuffing, password spraying, brute force, etc.
And the attacker can temporarily or permanently access the user's credentials if the target user has logged out of the session. After that, the attacker can access things like session IDs, tokens, URLs, and more.
Cross-Site Request Forgery (CSRF)
CSRF is a web application vulnerability where an attacker sends a fake request to a web page while the user is authenticated. In this case, the attacker changes the state of the attacked web application rather than performing data theft.
The main purpose of CSRF is to change the user's email ID, password, status, profile information, etc. The attacker gains complete access to the user's kun based on the action performed.
Sensitive Data Exposure
In this vulnerability, an attacker uses an encryption key to access and steal data. Exposure of sensitive data only occurs when something in the database is not stored correctly. Because of this, attackers can access data through various things such as weak encryption or data that has no encryption, transferring data between databases with incorrect practices/methods, etc.
By attacking these web applications, attackers can access things like banking information, health information, login credentials, etc. This can lead to identity theft, credit card fraud, etc.
XML External Entities (XXE)
XXE is a vulnerability that attackers use to block the processing of XML data of an application. Therefore, the attacker can access various things in the server and maintain back-end and external systems, and even users cannot access them in web applications.
This vulnerability results in disclosure of private data, server-side request forgery, etc.
Security Configuration Error
Security Configuration Errors can mean that the company is unable to implement security controls in the web application or implement all security controls with some errors.
Some configuration errors such as unencrypted files, unpatched systems, insecure devices, improper firewall protection, etc., allow attackers to access sensitive data or functions. Moreover, the attacker can also access the entire database.
Unsafe Deserialization
Insecure Deserialization is an attack aimed at web applications, where attackers can perform a large number of attacks such as DoS attacks, access control attacks, authentication evasion, repetitive attacks, etc.
For those who don't know serialization is a valuable process to convert objects in a format that can be subsequently recovered. Whereas deserialization is the opposite of serialization where data from a network file stream is retrieved to build objects again.
Use of Vulnerable Components
Some web application components such as frameworks, libraries, software modules, etc., may cause vulnerabilities. If in the use of such components the developer does not update them or is not aware of them, it will lead to an attack. The attacker can delete or take over all the data in the server.
Unvalidated Transfer and Forwarding
Various web applications can redirect or forward users to different URLs and pages within or across other websites. However, if the web application does not have a proper and effective validation system, then the user may receive incorrect inputs and be redirected to untrusted sources.
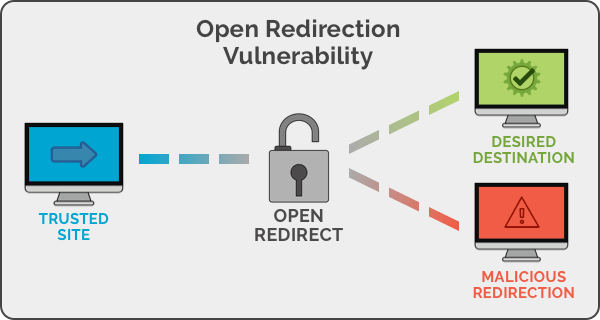
Source: gurutechnolabs
That's when attackers take advantage of the situation by changing the original URL into another URL to perform a phishing scam or obtain user credentials.
Inadequate Recording and Monitoring
When users forget to log out of important security-related events or such events are not monitored, this kind of vulnerability occurs at any time.
Attackers take advantage of this to retrieve a large amount of data and destroy it. In addition, attackers can also obtain important credentials from users.
Web Application Security Best Practices
The following are web application security practices that can be considered to prevent vulnerabilities in web systems/applications.
Web Application Data Encryption
Encrypting data is the oldest known way to secure a web application. Encryption is applied to all sensitive data in web applications, such as passwords, credit card details, demographic data, user data, etc.
Encryption is also applied to all data both data being sent (during data transactions) and data at rest, so that data can only be accessed by users who have the right permissions.
In addition to data encryption, companies must ensure to always update SSL certificates with the most recent / latest version, and web applications used must implement at least HTTPS security.
For authentication in web applications, it must be ensured that at least hashing algorithms have been implemented so that web application data protection is more efficient.
Monitoring Web Application Assets
It is important to monitor and know all the components used in and supporting the running of web applications to protect web applications.
Companies should have details of all the web application services used and details of the servers that contain the web application and its supporting components stored on those servers. This will help to know which assets are used to support the web application and save a lot of time in the long run.
Threat Assessment
Threat assessment is an important point in checking the security of web applications. It aims to identify potential threats that can threaten the security of web applications. The following are the steps that can be used to identify threats.
- Identify any pathways that allow an attacker to hack into a system or web application.
- Identify and list preventive measures against security attacks.
- Installing a tool to support the protection of web applications from the threat of attacks.
Conducting a thorough assessment can help companies integrate the best security measures that can be implemented in corporate web applications. However, if there is no internal support (support from upper management) and external support (implementing additional tools, hiring an IT security service provider, etc.), the information security of the company will not be guaranteed.
Avoid Security Configuration Errors
A structured development and deployment process can help integrate things in web applications efficiently. In addition, companies can test web applications that have been built before being applied to the company's business processes, and prevent various vulnerabilities that web applications have.
Adopting a Cyber Security Framework
A cybersecurity framework contains guidelines and practices to protect the information technology security of a company/organization. The guidelines or practices in the cybersecurity framework include security controls, risk assessment methods, practices/guidelines for defending data from attacks, and many more. Therefore, a cybersecurity framework is highly recommended to be adopted by companies/organizations.
Perform Software Quality Assurance and Testing
Quality assurance and extensive quality testing are best practices for web application security.
It is important for companies to manually test web applications based on applicable standards or frameworks, and add another layer of security to web applications to prevent security gaps in the process.
Quality assurance and testing can also improve user experience, prevent attacks, and improve brand image in the eyes of users or customers.
Update Dependencies Regularly
Changing scenarios must be accompanied by updating all running libraries and tools. If the company fails to do so, it can lead to the emergence of various web application security vulnerabilities. Not only that, companies will also face problems related to information security, performance, etc.
Therefore, it is important for companies to update their dependencies to the latest version to protect web applications from a large number of vulnerabilities, as well as improve performance and make maintenance tasks more efficient.
Web Application Vulnerability Prioritization
Prioritizing vulnerabilities is another web application security best practice. By prioritizing vulnerabilities, companies can know which vulnerability threats can be eliminated and the rest can be taken care of later.
There are five ways in which companies can prioritize vulnerabilities, which are as follows.
- Severity: Emphasizes critical and high-severity vulnerabilities based on CVSS (Common Vulnerability Scoring System) ratings.
- Application Type: Web applications that have sensitive data in them should be addressed first.
- Popularity: Priority can also be determined based on the popularity of the vulnerability among hackers.
- Completion Date: Determine the date of vulnerability resolution based on the level of vulnerability that has been set.
- Remediation: Based on the level of correction required, companies can prioritize vulnerabilities and address them. By using the most suitable method and focusing on a few vulnerabilities, companies can resolve them instantly and save time.
Reference:
https://www.helpnetsecurity.com/2020/04/07/threats-web-security/
https://www.gurutechnolabs.com/web-application-security/
Want to know more information, please visit our website at:
Don't forget to follow our other social media
Instagram : hdnmetatech
linkedin : https://www.linkedin.com/company/herdina-metatech-sinergi-corp
Facebook : Herdina Metatech Sinergi Corp